Policy & Regulation
-
Microsoft runs afoul of UK regulators again
The Competition and Markets Authority opened an antitrust investigation into Microsoft’s business software ecosystem on Thursday.
By Matt Ashare • May 14, 2026 -
Deep Dive
New cybersecurity industry coalition aims to lead US critical infrastructure protection
The new Alliance for Critical Infrastructure’s biggest goal: changing how the nation plans for a major cybersecurity crisis.
By Eric Geller • May 14, 2026 -
CISA adds Microsoft, ConnectWise vulnerabilities to active exploitation catalog
Russia has used one of the flaws, security experts said, while North Korea has used the other.
By Eric Geller • April 30, 2026 -
Vulnerability exploitation surges often precede disclosure, offering possible early warnings
Organizations can get ahead of major flaws with the right threat intelligence, according to a new report.
By Eric Geller • April 20, 2026 -
Sponsored by Cisco
Compliance is a competitive advantage for MSPs
Compliance pressure is intensifying, and expectations are getting firmer. Self-assertion is no longer enough.
April 20, 2026 -
FCC accelerates copper retirement gold rush
As the FCC makes it easier for carriers to turn off legacy lines, MetTel and other wholesale aggregators are stepping in to help customers migrate to digital systems.
By James Anderson • April 13, 2026 -
Retail and hospitality CISOs expect budget growth, new AI headaches and opportunities
More than eight in 10 security leaders in the sector say they’ve rolled out an AI governance framework to some degree, a new survey found.
By Eric Geller • April 2, 2026 -
UK regulators to probe Microsoft amid AI adoption surge
The Competition and Markets Authority will assess whether the tech giant’s software licensing practices reduce competition in the cloud market.
By Makenzie Holland • April 1, 2026 -
Citrix NetScaler products confirmed to be under exploitation
Security researchers at watchTowr warn that multiple flaws are involved in the early stages of a hacking spree that could rival the 2023 CitrixBleed campaign.
By David Jones • Updated March 30, 2026 -
Companies face difficult choices in blaming hackers for an attack
Publicly naming a hacking group can affect everything from retaliation to insurance coverage.
By Eric Geller • March 25, 2026 -
Trump AI policy provides a look at where legislation is headed
The White House’s AI framework provides Congress with a “wish list,” including putting courts in charge of copyright, according to one analyst.
By Makenzie Holland • March 23, 2026 -
Most organizations can’t actually recover from an identity attack: survey
More than three-quarters of organizations aren't testing identity disaster recovery at the recommended frequency — and nearly a quarter never test at all.
By Kelly Teal, Channel Dive contributor • March 13, 2026 -
Trump’s new cybersecurity strategy makes promises but lacks details
In a document released Friday, the administration vowed to increase the government’s use of AI for rapid cyber defense.
By Eric Geller • March 9, 2026 -
Deep Dive
How Microsoft, partners are tackling ‘huge, huge task’ of making security software safer
The technology giant and third-party security vendors are plotting an ambitious overhaul of how their products interoperate.
By Eric Geller • March 2, 2026 -
Global sovereign cloud spend to increase 35.6% in 2026
Cloud customers will seek more local infrastructure options in an effort to retain full control of their data, according to Gartner.
By Makenzie Holland • Feb. 11, 2026 -
Kyndryl reassures investors as revenue flattens
The IT services firm also revamped its finance team and commenced an audit of its cash management practices, company executives said Monday.
By Matt Ashare • Feb. 9, 2026 -
Oracle falls in line with Broadcom’s VMware license portability mandate
The hyperscaler follows AWS, Microsoft and Google Cloud in adopting the bring-your-own-license model for VCF cloud deployments.
By Matt Ashare • Jan. 23, 2026 -
IBM tackles cloud, AI sovereignty with new platform
Built on Red Hat's open source foundation, Sovereign Core aims to inherently provide control over the environment.
By Makenzie Holland • Jan. 15, 2026 -
Moody’s forecasts growing AI threats, regulatory friction for 2026
The U.S. and the EU continue to pursue starkly different regulatory agendas, the research firm noted.
By Eric Geller • Jan. 9, 2026 -
OpenText: MSPs need to think like business consultants
The MSP model is evolving as AI, cybersecurity threats and regulation reshape the channel.
By Christine Horton, Channel Dive contributor • Dec. 19, 2025 -
Gaia-X warns US hyperscalers about selling cloud sovereignty
Tech leaders at last month’s Gaia-X summit said sovereign branding can’t overcome the limits of what the cloud providers can offer European customers.
By Christine Horton, Channel Dive contributor • Dec. 19, 2025 -
Cybersecurity concerns are paramount among executives in almost all roles, regions and industries
A new survey finds widespread agreement that security is one of the biggest challenges facing companies today.
By Eric Geller • Dec. 18, 2025 -
CISA updates cybersecurity benchmarks for critical infrastructure organizations
The agency streamlines and supplements goals it first issued in 2022.
By Eric Geller • Dec. 12, 2025 -
Trump pledges order addressing patchwork of state AI laws
The move comes after the president and big tech unsuccessfully pushed for congressional action on the issue.
By Alexei Alexis • Dec. 9, 2025 -
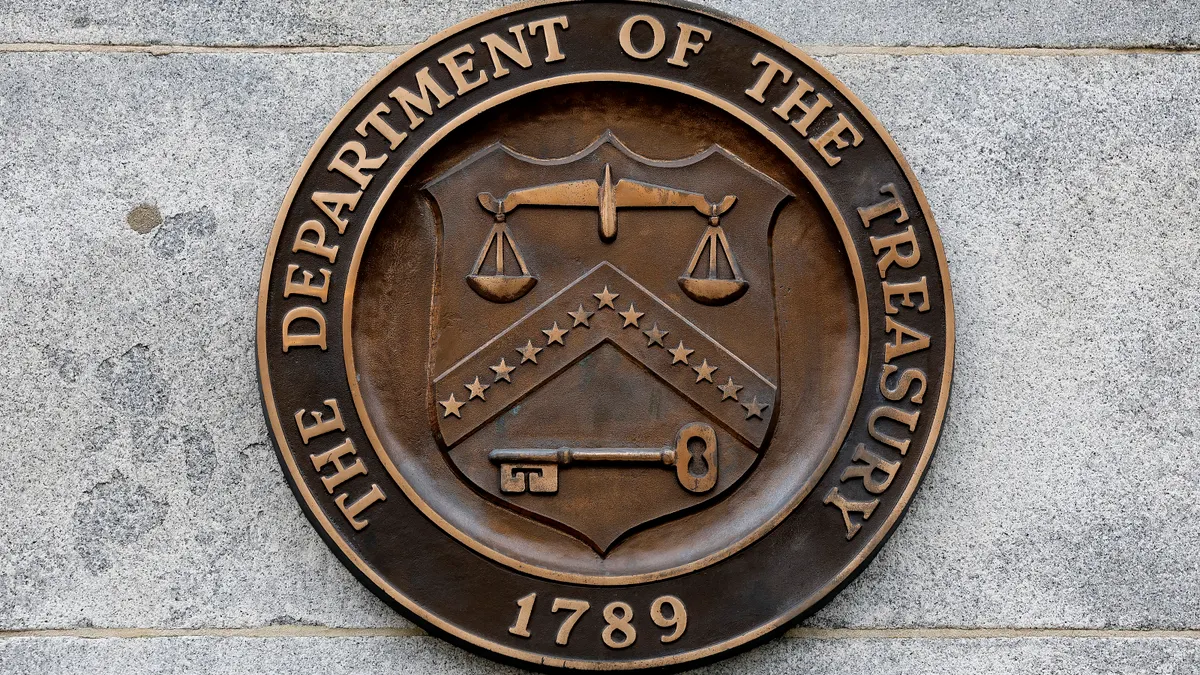
Ransomware peaked in 2023 prior to law enforcement actions
U.S. Treasury report shows drop in threat activity in the wake of aggressive takedown efforts.
By David Jones • Dec. 8, 2025